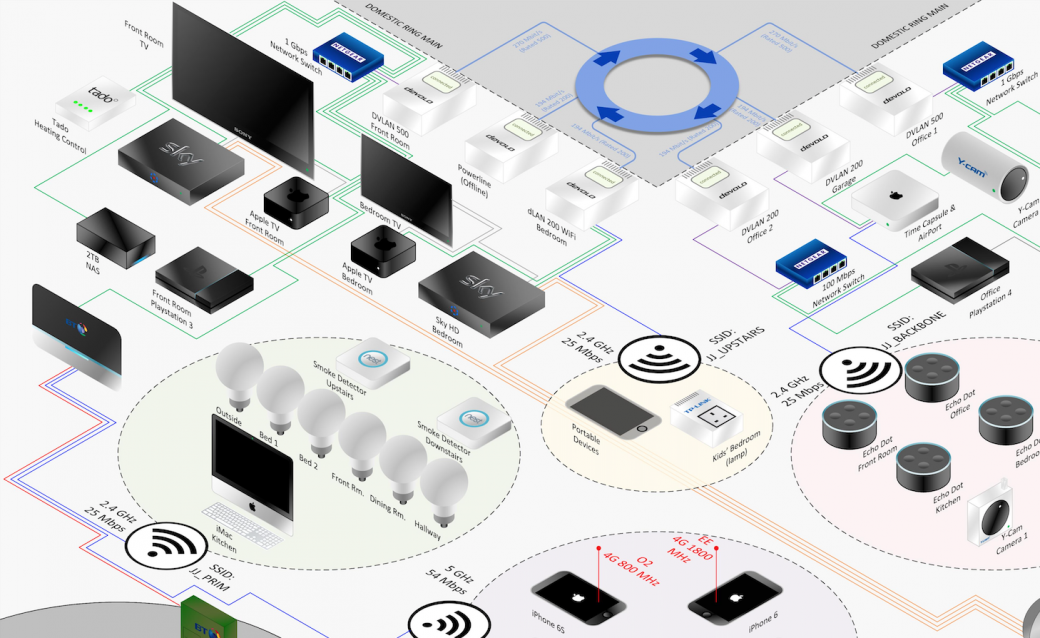
What happens when you take professional vulnerability scanning tools home? Is my home safe ? For the evaluation of the free scanning tools from Qualys and OpenVAS, I have performed some testing at home. It is a small network, with just over 30 network devices in the household: computers laptops, printer, phones, media players, routers and some home automation equipment. Here are eight things I learned from the experiment.
1. Unexpected open port
When I scanned my network from the outside, using my external IP address, I noticed some unusual open port. I found out that an application on my PC was opening and forwarding an administrative port on the outside using uPnP. My previous router did not have uPnP capabilities, and that is why I never noticed this before. Not only could this oversight result in unauthorized access to that application, it also could provide information about whether the PC is turned on or that nobody is in the house. I turned it off.
2. Default credentials for a managed switch
After a factory reset, I never changed the defaults on a Linksys switch. Luckily OpenVAS detected this. Although, it might have been a good thing after all. The switch uses the cleartext http protocol to transmit the username and password. A hacker on the network could be eavesdropping and obtain my password.
3. Kodi Local File Inclusion Vulnerability
I run Kodi on a Raspberry PI as a media player. The remote web interface has a feature to display thumbnails of the media files. A bug in this feature causes allows access to file on the sd-card of the Raspberry. In general this might not be a huge problem at home, but it is a vulnerability nonetheless.
4. Hardware firmware out of date
The firmware of a router is outdated, and newer versions are available. This would allow remote attackers to perform several interesting attacks: one click on one email would give a hacker access to the router. I’m not using that router as a router anymore, but I certainly need to update the firmware anyway.
5. SMB
A whole set of vulnerabilities is linked to the use of Windows Server Message Block (SMB ) on several devices and computers. Most issues can be patched, but often this causes difficult to trace compatibility issues between storage devices, computers and media players. I hope this will get better in future. Back to good old NFS?
6. SSH/SSL Weak encryption algorithms
A couple of devices and my Linux computer can be accessed using SSH. A number of encryption algorithms which were considered secure a couple of years ago, should not be used anymore. I keep my Linux machines pretty well updated, but the weak algorithms that are available by out of the box need to be disabled manually. A good reminder to do some serious hardening before allowing connections from the internet.
7. Adobe Flash update
Qualys Cloud Agent is extremely fast in reporting out of date software. I got a warning the day after a new release came out. I do not need to use Flash often, but it seems every time I do, I need to download a new version. Fortunately, HTML5 introduces a new way of embedding video and audio.
8. Information gathering and false positives
Both tools give a lot of results requiring investigation. A scan reveal a lot of information about the network. It takes some time and expertise to figure out what vulnerabilities are acceptable, what cannot be avoided, and what should be fixed.